Router-Exploit-Shovel is an automated application generation for Stack Overflow types on Wireless Routers.
Router exploits shovel is an automated application generation tool for stack overflow types on wireless routers. The tool implements the key functions of exploits, it can adapt to the length of the data padding on the stack, generate the ROP chain, generate the encoded shellcode, and finally assemble them into a complete attack code. The user only needs to attach the attack code to the overflow location of the POC to complete the Exploit of the remote code execution.
The tool supports MIPSel and MIPSeb.Run on Ubuntu 16.04 64bit.
Router-Exploit-Shovel's Installation
Open your Terminal and enter these commands:
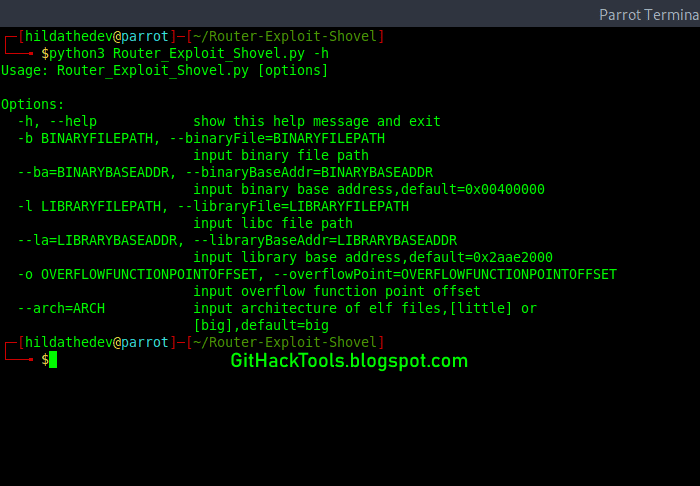
Usage
Example:
python3 Router_Exploit_Shovel.py -b test_binaries/mipseb-httpd -l test_binaries/libuClibc-0.9.30.so -o 0x00478584Router-Exploit-Shovel's screenshot
Code structure
ROP chain generation
This tool uses pattern to generate ROP chains. Extract patterns from common ROP exploitation procedure. Use regex matching to find available gadgets to fill up chain strings. Base64 encoding is to avoid duplicate character escapes. For example:
Attackblocks
You can get attackblocks generated in results/attackBlocks.txt. Such as:
You might like these similar tools:
- eXpliot - Internet Of Things Exploitation Framework
- RouterSploit: Exploitation Framework for Embedded Devices
More information
- Nsa Hack Tools
- Growth Hacker Tools
- Pentest Tools Free
- Pentest Recon Tools
- New Hacker Tools
- Hacks And Tools
- Hack Rom Tools
- Nsa Hack Tools
- Hacker Tools Mac
- Hacking Tools Download
- Install Pentest Tools Ubuntu
- Bluetooth Hacking Tools Kali
- Pentest Tools Tcp Port Scanner
- Pentest Tools Find Subdomains
- Hack And Tools
- Hacker Tools Github
- Hak5 Tools
- Hacking Tools For Windows
- Hacking Tools For Mac
- Pentest Tools For Mac
- Growth Hacker Tools
- Hacker
- Hacking Tools For Beginners
- Underground Hacker Sites
- Hacker Tools Windows
- Hack Rom Tools
- Pentest Tools Android
- Pentest Tools Alternative

No comments:
Post a Comment